Combined with DNS-over-TLS and DNS-over-HTTPS, Technitium DNS Server provides a good level security and privacy from network level DNS attacks and from adware. This makes it a must have tool if you are a privacy and security conscious person.
Technitium DNS Server is cross platform and works on Windows, Linux or macOS.
 |
| Technitium DNS Server v2.0 |
How Does It Work?
The Ad blocking feature works using the DNS Sinkhole method. With this feature enabled, for all the blocked domain names, the DNS Server will respond with 0.0.0.0 IPv4 address and :: for IPv6 address making the Ads fail to load making the website you visit free from Ads. This can not only block Ads but also adware, malware, social networks, porn etc. based on the block lists you configure in settings.
On your computer, you need to install the DNS Server and configure your network adapter's DNS settings to use the locally hosted DNS server. Once this is done, you need to configure the Block List URL settings to start blocking Ads. Once the DNS Server loads the block lists, it would respond with 0.0.0.0 IP address for the blocked websites making them fail to load.
You may also install the DNS Server on any spare computer on your network and configure your home or office router with IP address of this spare computer as DNS server in DHCP settings. With this setup, all your computers and devices like mobile phones would use the installed DNS Server blocking Ads and malware domains on all devices without installing any additional software on them.
Configuring Block Lists
To enable Ad blocking, you need to configure Block List URLs in the settings. Known and popular block lists are already listed in the Quick Add drop down list from where you can just click and add those URLs.
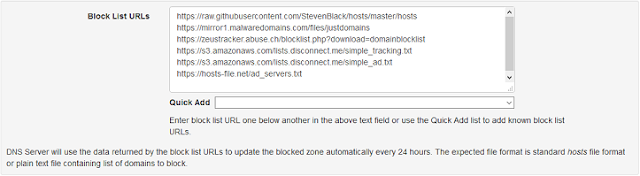 |
| Technitium DNS Server Block List Configuration |
If you are not sure, just select the Default option from the Quick Add drop down list and a default set of block list URLs would get configured.
Once done, click the Save Settings button at the bottom of the page to save the changes and start the block list download background process. These configured block lists are automatically downloaded every 24 hours to keep the DNS Server blocked zone updated.
If you have the DNS server installed directly on your computer then don't forget to configure your network adapter's DNS server settings to 127.0.0.1 (for IPv4) and ::1 (for IPv6). Without these network configuration changes, the DNS Server wont get any queries to respond to and things wont work as intended.
If you setup the DNS server to be used on the network by all devices then do configure your router's DHCP config and set the IP address of the computer running the DNS server as the DNS for your network. By configuring the router's DHCP, you don't need to manually configure any of your devices on the network.
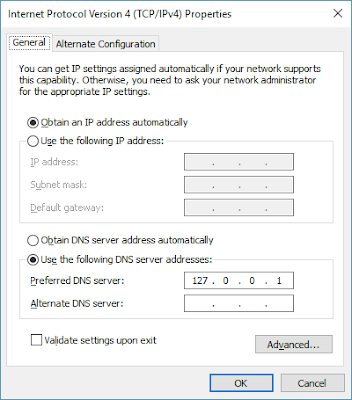 |
| IPv4 DNS Server Network Configuration |
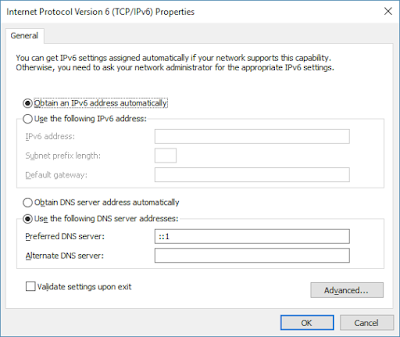 |
| IPv6 DNS Server Network Configuration |
That's It!
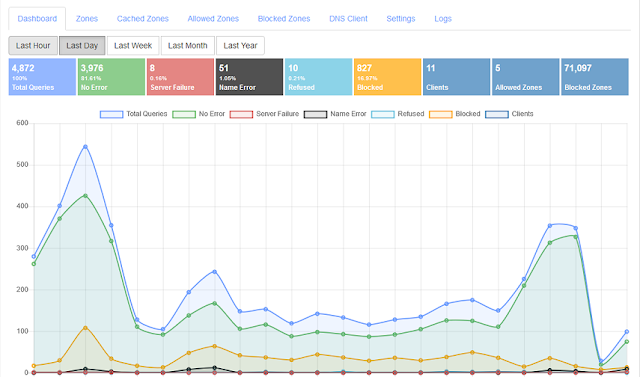
Once the configuration is done, just check the Dashboard on the web console after a couple of minutes to see the number of blocked domains in the Blocked Zones widget. If there are too many block list URLs configured, it may take few more minutes for all of them to get downloaded and loaded.
If you have any further queries, do write them below as comments or send an email to support@technitium.com.
Question: As a developer - and a lazy developer at that - I've previously used my own little bash-scripts to populate my hosts-file in linux. In Windows I've formerly tried to use Acrylic DNS with little to no success.
ReplyDeleteThis, however, works right out of the box - which is fantastic!
I, however, have a question: Would it be possible to import my own dev-redirects the same way as I today can import or add my own domains to block via blocklist.txt on the local webserver?
I had a quick peek at the source code and it really isn't my preferred language, but... Am I correct in assuming it's a case of using the provided IP-address instead of replacing it with the sinkhole 0.0.0.0?
Thing is; I keep lists in simple hosts-format (ip domain) which are updated script-wise according to my location - and thus dhcp-provided ip-address.This way I would be able to run a very script which inserts my local ip-address on current location into said list(s).
The alternative is, I guess, to enter several A-records in my zones and extending the TTL for the different ip-series accordingly, 1800 for work, 3600 for home, 7200 for public, etc.
TL;DR:
Excellent piece of software, would appreciate possibility to import dev-server lists.
Thanks for the compliments. The block zone implementation in the DNS Server will use domain names from the block lists and always use 0.0.0.0 IP address to sinkhole the domain name.
DeleteTo use domain names for development/production testing scenarios, you can add the domain as a Zone in the DNS Server. You can then set Type A records for IP addresses and then enable/disable individual records or you can disable the entire zone. When zone is disabled, the DNS Server will return records from the actual name server hosting the domain name in production.
You can easily automate this by using the REST API that the DNS Server web console itself uses in its javascript code. If you have any queries or need any more details, do let me know over email at support@technitium.com.
Is there a way to white list certain domains from the block list?
ReplyDeleteYes, you can add your domains in the Allowed Zones to override the block list.
Deleteusing this app and working well, however the log file dates are an hour out. I'm in the UK so I'm guessing it's not taking into account the DST of +1.
ReplyDeleteIf somehow it can use the time of the host computer in the logs, it would be appreciated.
Having to remember to add an hour on is easy enough but makes it hard when tracking requests.
Many thanks
Thanks for the feedback. The date time in logs is in UTC and not GMT so, it does not have daylight saving. I am planning to have some option to set the timezone for logging in next update.
DeleteHi,
ReplyDeleteCan I redirect 0.0.0.0 to specific url or ip for custom error message ?
Great software !!!
regards
Sam
Technically you can return any IP address from the DNS server instead of 0.0.0.0 for blocked domain names but, practically it wont work.
DeleteThis is since most websites nowadays are served over HTTPS and thus you wont be able to show custom error message for most websites. If you implement it then users will mostly see SSL certificate error notices instead of your custom error page.
Secondly most blocked items are Ads that are loaded using iframes and that space will too show SSL errors and create a mess.
Ok, thanks !
DeleteSam
Hi, I am experimenting with the Ad-blocking for my own local network, but so far, only the computer that I installed the server application has access to the internet, no other devices in my network can access the internet.
ReplyDeleteI have change my router's DNS server to use the computer's address with the application installed and I have configure this computer (the one that's currently working) to use loopback address.
I wonder are there any steps I'm missing or any settings I might forgot to configure?
Best regards
Keaw
Thanks for the comment. If you have DNS server installed on Windows then you will need to manually add a firewall rule for TCP and UDP port 53. Next release for DNS Server will do this step automatically. If its still not working then do send an email to support@technitium.com with details of your config.
DeleteHi again
DeleteThank you for your suggestion, I have just tried it with my server and it appears that the problem has been fixed!
Thank you very much! This is definitely one great software
Best regards
Keaw
Hello!
ReplyDeleteThe Technitium DNS Server is a fantastic piece of software, and I've been using it for the last several months, with great luck. Thank you for developing it!!
I am running the DNS Server on a Rasberry Pi 2B+, and it generally ran error-free.
However, I recently changed the RasPi to also provide WINS service on my network, and so I installed SAMBA (both smbd and nmbd) and configured it to serve as the Domain Master Browser.
Ever since I did that, I've been struggling with some configuration issues, where the Logging Data (the stats that show up on the Dashboard) have dropped to ZERO. Normally, in the past, it has tracked somewhere between 20,000 and 40,000 queries per day.
I have been fiddling with the settings, and have managed to both "break" it and "fix" it a couple of times...but I'm still back to the situation where it is no longer logging/tracking the queries that it is serving.
Is there some sort of binding on the interface that I've broken (by introducing the smbd/nmbd services) which could be interfering with the DNS Server's ability to track the queries it's serving?
I'm a little lost. I /thought/ I understood what I was doing, but it seems I am unable to get my system back to "the good ol' days" when it was just happily and reliably serving queries, trapping/sinkholing the blocked domains (to kill ads), and *accurately* tracking the metrics of its service.
Any pointers, thoughts, and/or tips for getting it back to "showroom" state?
(Put another way, am I going to be reduced to wiping the OS, reinstalling, and rebuilding the DNS Server software?)
I was hoping that there was some vestige of the guide for how the settings are initialized, but I couldn't find it.
Many thanks, in advance!
Mike R.
Hi, Thanks for the feedback. I would suggest that you take a look at the logs being generated by the DNS server. It would indicate any issue that is the cause. If you would like to get help in analyzing the log file then do send them with details of your config to support@technitium.com.
DeleteThanks for the speedy reply!
DeleteI took a quick glance through the logs, and I see a *WHOLE LOT* of entries like the following:
/-/-/-/
[2020-05-10 23:59:50 UTC] DNS Server recursive resolution failed for QNAME: outlook.ms-acdc.office.com; QTYPE: A; QCLASS: IN;
TechnitiumLibrary.Net.Dns.DnsClientException: DnsClient failed to resolve the request: no response from name servers.
---> System.IO.IOException: Unable to write data to the transport connection: Broken pipe.
---> System.Net.Sockets.SocketException (32): Broken pipe
at System.Net.Sockets.NetworkStream.Write(Byte[] buffer, Int32 offset, Int32 size)
--- End of inner exception stack trace ---
at System.Net.Sockets.NetworkStream.Write(Byte[] buffer, Int32 offset, Int32 size)
at System.Net.Security.SslStream.WriteSingleChunk[TWriteAdapter](TWriteAdapter writeAdapter, ReadOnlyMemory`1 buffer)
at System.Net.Security.SslStream.WriteAsyncInternal[TWriteAdapter](TWriteAdapter writeAdapter, ReadOnlyMemory`1 buffer)
at System.Net.Security.SslStream.Write(Byte[] buffer, Int32 offset, Int32 count)
at TechnitiumLibrary.IO.WriteBufferedStream.Flush() in Z:\Technitium\Projects\TechnitiumLibrary\TechnitiumLibrary.IO\WriteBufferedStream.cs:line 99
at TechnitiumLibrary.IO.WriteBufferedStream.Write(Byte[] buffer, Int32 offset, Int32 count) in Z:\Technitium\Projects\TechnitiumLibrary\TechnitiumLibrary.IO\WriteBufferedSt
ream.cs:line 166
at TechnitiumLibrary.Net.Dns.ClientConnection.TcpClientConnection.Query(DnsDatagram request) in Z:\Technitium\Projects\TechnitiumLibrary\TechnitiumLibrary.Net\Dns\ClientCon
nection\TcpClientConnection.cs:line 239
at TechnitiumLibrary.Net.Dns.DnsClient.Resolve(DnsDatagram request) in Z:\Technitium\Projects\TechnitiumLibrary\TechnitiumLibrary.Net\Dns\DnsClient.cs:line 1156
--- End of inner exception stack trace ---
at TechnitiumLibrary.Net.Dns.DnsClient.Resolve(DnsDatagram request) in Z:\Technitium\Projects\TechnitiumLibrary\TechnitiumLibrary.Net\Dns\DnsClient.cs:line 1174
at TechnitiumLibrary.Net.Dns.DnsClient.Resolve(DnsQuestionRecord questionRecord) in Z:\Technitium\Projects\TechnitiumLibrary\TechnitiumLibrary.Net\Dns\DnsClient.cs:line 117
9
at DnsServerCore.Dns.DnsServer.<>c__DisplayClass71_0.b__0(Object state) in Z:\Technitium\Projects\DnsServer\DnsServerCore\Dns\DnsServer.cs:line 1205
/-/-/-/
Which has a bunch of gobbledy-gook I can't really understand...although I see a bunch "IO Exception" tags. I am worried this may mean that my SD Card has got one foot (if not two) in the grave.
Do you see anything else (from the snippet) which might point to anything else?
Again, many thanks!!
[I will follow up with an email to the support box, as well. Thx!]
Cheers,
Mike R
Thanks for the details. The error log just means that the SSL network connection used by the DNS server was closed due to timeout and it just concludes that there was no response from the forwarder server. So, no issues with your SD card.
DeleteI've finally started diving into whole home network adblocking, because browsing on my phone drives me nuts.
ReplyDeleteI have a dedicated windows 10 server that runs PLEX, makes data backups for all of my computers, and is running 24/7. I'm not interested in adding any additional hardware like a pi, as this is simple as hell and just works.
I started w/ pi-hole in a docker container, and I was having major reliability issues to the point that it's dead to me. I can't get those hours back and I don't want to try.
So, on to Technitium DNS. Holy crap the setup on this was simple. Why it doesn't get mentioned more is beyond me. I've got it up and running with my USG, and so far it seems to be working great.
My questions are as follows, what settings should I enable/disable to make this as secure, reliable/wife approval factor, and low maintenance as possible?
For instance, should I enable the following settings?
Enable HTTPS
Enable HTTP to HTTPS Redirection
Enable DNS-over-HTTP
Enable DNS-over-TLS
Enable DNS-over-HTTPS
Thanks for the compliments. You got it working well already and most things work well with the default settings.
DeleteFor the settings that you asked:
- Enable HTTPS: This will enable HTTPS for the web console. It requires a valid TLS certificate to work. Its useful if you want to access the DNS server web console over the Internet.
- Enable HTTP to HTTPS Redirection: This will redirect the web console request to HTTPS url if HTTPS is enabled.
- Enable DNS-over-HTTP, Enable DNS-over-TLS, & Enable DNS-over-HTTPS: These options are to allow hosting your own DNS service for these protocols just like how Google or Cloudflare runs their DNS services. You do not need to enable these settings to consume these protocols. If you want to just use Google or Cloudflare DNS service then you can just configure them as a forwarder in the settings.
If you have any more queries then do send them to support@technitium.com.
Thanks for the feedback. I will get this option added in next update.
ReplyDeleteSo, due to one critical bug, I had just released v6.2 which adds this feature to return NXDOMAIN. Just check the settings near the option to setup block list URLs. Let me know if that worked for you.
ReplyDeleteGood day, I have been looking for an amazing DNS server like this.
ReplyDeletePlease am new to the configuration, am running this server in a school for students and I would like to block all websites and allow access to only specified websites. Thanks
Hi. Thanks for the compliments. You can block all domain names by adding "*" to the Blocked tab on the web panel and then add the domains you want to allow in the Allowed tab. Maintaining this could be tricky since websites use a lot of 3rd party resources and so you will have to allow all the other domain names that are used by the website to make it load correctly.
DeleteHow do I whitelist an IP so that it doesn't get any links blocked on it
ReplyDeleteYou can only block or allow domain names using DNS server. For IP addresses you will need to use firewall.
DeleteHow can I make this apps on Win11 to auto start after I reboot my computer or just power my machine?
ReplyDeleteIf you have installed using the Windows setup then it will start automatically by default.
DeleteHi there, so far im loving technitium dns serrver.
ReplyDeleteIs there any file where i can dump all my exported gravity blocklist from pihole in a txt, other than the import on the blocked in the gui.
thanks in advance
You don't need to export it in the Blocked section in GUI. Just switch to Settings > Blocking section where you can enter the exact same block list URLs from your pihole and it would work as expected.
DeleteHello there,
ReplyDeleteTechnitium DNS works great at blocking ads, however, it leaves 'Refused to connect' placeholders on place of blocked ads.
Any way to make them disappear? Like uBlock Origin?
Thanks for asking. This is not possible with DNS level blocking so you will need to rely on browser based blocking plugins that can access the web page content and remove items from them. Its recommended to use both DNS and browser blockers together to have optimal blocking.
DeleteI just thought that I could find or set website with empty page on it and set it in Custom Blocking Addresses in Blocking Type, but it seems it's for something else.
DeleteYou can install the Block Page app which can display a webpage when a domain name is blocked which is configured by setting the IP address of the server as the Custom Blocking Address. However, since most websites today use HTTPS, you will see SSL errors instead of the "Refused to connect" page which will need you to accept the error before the blank page is shown.
DeleteI was looking for a well featured but easy to configure DNS for docker compose deployment. Oh man, what a great software this is. I'm glad I found and installed it. I'm considering permanently replacing the pfSense DNS for easy configuration and monitoring while performing well under high load. Thank you for creating and maintaining this gem!
ReplyDeleteThanks for the kind words.
DeleteThanks for the compliments.
ReplyDeleteHey, thank you so much for making this! Pihole was such a pain to get running on windows, and your way works much faster! I wouldn't be surprised if it worked better then Pihole on linux too. Just wondering, is it possible to see the domains being connected too, and not just the number? Is there also a way to see which app/software is connecting to which domains (such as chrome is doing this, and explorer.exe is connecting to that. Thanks in advance.
ReplyDeleteThanks for the compliments.
DeleteYes, you can install the Query Logs (Sqlite) app from the Apps section and then use the Logs > Query Logs section to query with filters. Its not real time though since you will need to click to get results. There is also option to enable query logging in Settings > Logging section.
Its not possible to identify program/application since for most apps, its the OS that does DNS resolution. Even if the app does DNS resolution by itself, the DNS server cannot find out the app details since the requests are received over network.
Is it possible to add wildcards/or regex to Technitium?
ReplyDeleteIf you are asking about blocking feature then yes you can do that by using the Advanced Blocking DNS app.
Deleteola temalgum video de como configurar a pagina de bloqueio do dns.
ReplyDeleteSe você está perguntando sobre o aplicativo Block Page, então não há vídeo/documentação disponível para ele. O aplicativo block page ou qualquer configuração similar também tem a limitação de que o usuário vê erros SSL/TLS quando você tenta mostrar a página de bloqueio quando o nome de domínio está bloqueado. Então não é realmente de muita utilidade, a menos que você precise tê-lo devido a regulamentações governamentais.
DeleteThank you for making this! Is it possible to use this in conjunction with AcrylicDNS?
ReplyDeleteYou're welcome. Yes you can configure your Acrylic DNS to forward to your local DNS setup. But, you can install Technitium DNS directly on your laptop too so that you wont need anything else.
DeleteI'm running into issues with setting up advanced blocking. Is there some sort of logging or documentation I can look through to make sure I'm setting this up properly?
ReplyDeleteThanks for asking. There is no docs available for the app but you can send your queries to support@technitium.com or post on reddit.com/r/technitium to get help with it.
DeleteGreat product but how setup that for mobiles on 4G ?
ReplyDeleteDoes this solution offer same benefit as NextDNS ? I use them as my mobiles on roaming can use those DNS
I would prefer running DNS at home if knew how manage my roaming devices.
You will need to setup the DNS server on either a VPS or with a static IP on your home broadband. Using VPS is recommended since its cheap and you wont have to worry about downtime caused due to power failures or Internet issues.
DeleteTake a look at this blog post which explains how to do such a setup in details: https://blog.technitium.com/2020/07/how-to-host-your-own-dns-over-https-and.html
I have just run into your Technitium DNS Server project and I will soon install via docker and play around. I am also fascinated/obsessed with Openwrt and how powerful it is. I was wondering if Technitium DNS Server could be installed on openwrt and did a little bit of digging and it looks like it is possible, but may be a little beyond my attention span/skill level. I was wondering if you have ever considered a version that would run natively on openwrt?
ReplyDeleteThank you for creating an awesome project that makes digital life better!
Thanks for the compliments. Since Openwrt is Linux based, its possible to install DNS server on it. You just need to install .NET Runtime and use the install script that is already available to install it. You will need to install .NET Runtime manually by downloading the tar.gz file for the platform and extract it somewhere like /opt/dotnet and create a link for it using "ln -s /opt/dotnet/dotnet /usr/bin" command.
DeleteHi, big fan of Technitium. I used a community script for Proxmox to set the container, so I could solely focus on all DNS-related settings. Needless to say, I'm enlightened, and I am glad I decided to "risk" the deep dive into the unknown solution rather than pick something like PiHole, even though my main use case is ad blocking.
ReplyDeleteNow I also utilise Technitium (along with a reverse proxy) to smoothly switch between various services in my home lab via local hostnames. It's great!
However, I'm facing issues with my Android phone. It's the only device that stubbornly refuses to use my DNS for some reason. I'm aware of Chrome preferring its own services and potential misconfiguration of WiFi settings, but I've checked everything: various browsers, DNS1 and DNS2 pointing to my home DNS, even pinging the local hostname in the terminal works. However, when I use ANY browser, it just doesn't resolve... The only exception is when I'm also connected to my home VPN. And that's just the phone; my other Android tablet works.
Do you have any idea what is going on or where I should seek help?
Thanks for the compliments. I am not sure what could be the issue with your Android phone. It should be some issue with the config for sure since there is no issue otherwise with Android devices. How is the phone connected to the network: is it using router's DHCP server or the Technitium DHCP server that is built-in? Have you configured private DNS?
DeleteYes, I use my router's DHCP. I haven't tested Technitium's DHCP, but I'll give it a read. Private DNS is disabled, since I don't use TLS.
DeleteA little funny, but since asking here, I picked up a lead. It looks like the system sets DNS2 to 8.8.8.8, even though it's clearly stated by the DHCP that it should use the same IP for both. Perhaps the same IP for both DNS is unacceptable in my Android?
Thanks for the clues. I have a lot to experiment with again.
You can just configure a single DNS IP address in your DHCP server config. Android uses only configured DNS servers as per I observed in tests.
DeleteHi thank you for this great piece of software but i need help with a problem
ReplyDeletei have it installed as a vm on proxmox and chose it as dns in my pfsense, the problem is:
1- technitium resolves names and shows up with the nslookup command on client pc but also resolves ads websites (i selected some blocklists from the menu).
2- technitium (the same server) resolves names and block ads and blocklist websites when i bypass pfsense (on my phone) and manually set the address of the server.
can you please pinpoint where i am wrong?
1/Technitium server ip as dns in pfsense ( System/General Setup)
2/behaviour: use remote dns server, ignore local
3/Rule: PASS/LAN/IPV4/TCP+UDP/ANY/DNS to Technitium IP on DNS port 53
4/Kea DHCP Technitium ip in DNS servers
5/ DNS Forwarder: Disabled
6/ DNS Resolver: Disabled
Thank you
Thanks for asking. Do you have any secondary DNS server IP configured with pfsense? If yes then the ad domain names may be getting resolved using the secondary DNS.
DeleteIn any case, it is recommended to always assign the DNS server's IP address directly (using DHCP) to all clients instead of using a middlebox as the DNS proxy. This way, you get to see stats for each user on the DNS dashboard and also removes some common issues that some middlebox DNS proxies have.
Thank you for responding
Deletei have only one instance of technitium. Could it be that pfsense is resolving these ad websites via the isp router? (which is the default gateway)
Yes, that is more likely since your direct tests with Technitium DNS server confirms that its blocking ad domain names.
Delete